As organizations move to cloud, distributed systems, and AI-powered environments, the traditional boundary has dissolved. Security now depends less on where your network ends and more on who (or what) is trying to access what, under which conditions, making identity the new perimeter.
But while infrastructure has evolved, many identity programs have not. As organizations scale across cloud and hybrid environments, they often inherit a fragmented identity ecosystem with multiple IAM tools, inconsistent policies, and limited visibility. Those gaps create exactly what attackers want: weak points in the identity fabric that can be exploited quietly and repeatedly.
Attackers are taking full advantage of this situation. Over 80% of breaches now involve compromised credentials, and identity attacks continue to rise year on year. The question is no longer whether you can prevent unauthorized access in isolated systems. The real question is whether your entire identity fabric is resilient enough to withstand next‑generation threats amplified by AI, scaled by automation, and accelerated by a mature cybercrime economy.
“Identity fabric is a unified framework that integrates and orchestrates multiple identity and access management systems to provide seamless, secure, and centralized control across modern infrastructure.”
The three forces breaking traditional IAM models
Identity threats are evolving rapidly. Organizations must assume adversaries will target identity because it offers the most efficient path to access, privilege escalation, and persistence often while appearing legitimate.
The visibility gap created by fragmented identity environments is now being intensified by three converging trends:
- Explosion of machine identities: Non-Human Identities (NHIs) such as service accounts, bots, and APIs now outnumber human identities by a factor of eight to one. These identities often hold elevated privileges but lack the robust protections (like MFA) applied to humans, creating a massive, unmonitored attack surface.
- AI as a threat multiplier: Artificial Intelligence is reshaping the threat landscape. 30% of organizations have already experienced an AI-generated identity incident. Attackers use AI to scale social engineering and create sophisticated deepfakes, making traditional detection methods obsolete.
- Credential brokerage: The cybercrime economy has specialized. “Access Brokers” now harvest and sell credentials, allowing attackers to simply log in rather than hack in. The widespread use of infostealers means that a single infection can compromise an entire organization’s identity posture.
How to build a resilient Identity Fabric: A practical framework
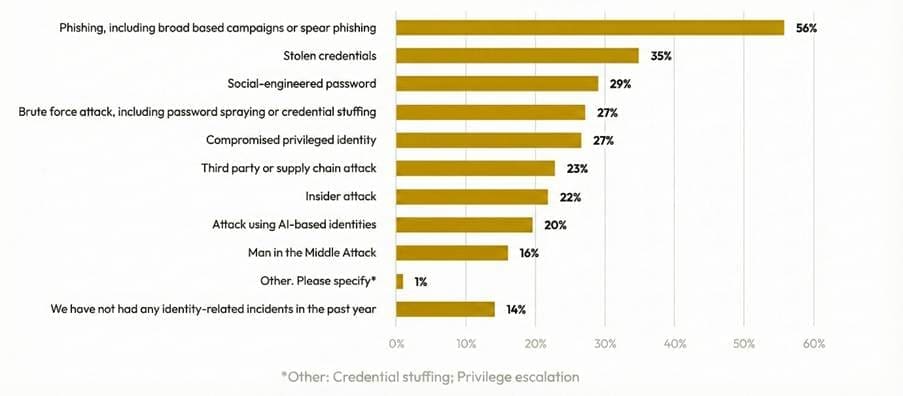
According to the Identity Designed Security Alliance (IDSA) 2025 survey for trends in identity security, when asked what kind of identity-related incident your company had last year following was the response reaffirming the risks are real:
So, the question is how to create a tightly knit and resilient identity fabric that provides comprehensive visibility, continuous monitoring, and automated response capabilities?
- Understanding the gaps and creating a strategic roadmap: Conducting a detailed current‑state assessment aligned to global best practices, regulatory requirements, and the organization’s threat landscape is the most critical first step.
Once the risks are identified and prioritized, organizations must create a strategic, time‑bound roadmap aligned to business priorities and regulatory expectations.
- Strengthening the core: While implementing missing controls identified during the assessment is crucial, it is equally important to revisit existing controls to ensure they are fully deployed, optimized, and delivering maximum coverage.
All controls should be integrated with relevant solutions in identity fabric. For example, two‑way integration between Identity Governance (IGA) and Privileged Access Management (PAM) solutions. This integration is frequently overlooked.
- Adaptive and Extended MFA: The era of simple SMS-based MFA is over. Microsoft reports that multifactor authentication still blocks over 99% of unauthorized access attempts, but the type of MFA matters.
Phishing-resistant MFA: Organizations must migrate to FIDO2 keys or certificate-based authentication to counter AiTM (Adversary-in-the-Middle) and social engineering attacks.
Adaptive Policies: MFA must be dynamic. Using “Conditional Access,” the system should demand stronger proof of identity if the risk level rises (e.g., access from a new device or high-risk IP)
Extending the MFA: MFA should be extended to all possible systems also to legacy systems using MFA Proxies/Gateways or Network layer enforcements.
Advisory note: The Central Bank of the UAE (CBUAE) has issued a significant directive requiring all licensed financial institutions (LFIs) to phase out SMS and email-based One-Time Passwords (OTPs) by March 31, 2026. The directive mandates a shift to more secure, modern Multi-Factor Authentication (MFA) methods, primarily app-based authentication and biometrics.
All organizations should adopt this for better security even if not mandated by any regulations.
- Identity Visibility and Intelligence Platforms (IVIP): Gartner predicts that by 2028, 70% of CISOs will utilize an Identity Visibility and Intelligence Platform (IVIP) to shrink their IAM attack surface. An IVIP acts as the “brain” of the identity fabric. It sits above the fragmented IAM tools, ingesting data to provide a unified view of all identities (human and machine), entitlements, and risk postures.
By adopting IVIP, organizations can:
Discover hidden risks: Identify orphaned accounts and over-provisioned machine identities that traditional IGA tools miss.
Prioritize remediation: Use AI-driven analytics to focus on the highest-risk vulnerabilities first, rather than drowning in alerts.
- Identity Threat Detection and Response (ITDR): While IVIP provides the map, ITDR provides the radar. ITDR tools are essential for detecting attacks in real-time, such as token theft or Adversary-in-the-Middle (AiTM) attacks, which can bypass standard controls. A resilient fabric uses ITDR to continuously monitor the “hygiene” of the environment and detect anomalies like a user logging in from an impossible location or a service account suddenly accessing sensitive data.
- Integration with MDR and automated response: Speed is the defining factor in resilience. To achieve this, the Identity Fabric must integrate with Managed Detection and Response (MDR) and SOAR (Security Orchestration, Automation, and Response) platforms.
Automated containment: When an ITDR tool detects a high-fidelity threat (e.g., a “Golden Ticket” attack), the fabric should automatically trigger a response suspending the compromised account or revoking the session token without waiting for human intervention
Feedback loops: Data from the MDR team should feed back into the IVIP, updating policies to prevent future occurrences of the same attack vector.
Beyond these measures, organizations should also monitor the dark web for signs of compromise, detect impersonation attempts such as fake social profiles or cybersquatting, and extend identity visibility across the supply chain wherever feasible.
How CPX can help build a resilient Identity Fabric
The threat landscape is unforgiving and evolving. This commands a shift in strategy and building resilience, which requires more than isolated tools. It demands a unified, Identity Fabric‑led approach that governs human and non‑human identities together, integrates real‑time threat detection, and enables rapid, automated response. Identity must operate as the primary control plane for Zero Trust, adapting continuously to risk and context.
CPX supports this shift by delivering end‑to‑end, identity fabric‑led architecture combining strategy, implementation, and 24×7 operations to help organizations build a resilient, compliant, and future‑ready identity foundation.
Reach out to our team for details.
References:
- IDSA 2025 Trends in Identity Security
- Microsoft Digital Defense Report 2025
- Gartner.com