14 January, 2026

Cybersecurity in 2026 has entered a defining phase. The way we think about trust, identity, and resilience has fundamentally changed. Across the MENA region, enterprises and governments are standing at a turning point. Digital transformation is accelerating. AI adoption is becoming mainstream. Data is now viewed as a national asset. And adversaries are evolving even faster.
Today, the question for leaders is no longer if they will be targeted, but how ready they are when it happens and how fast they can respond and recover from an incident.
One of the clearest shifts we’re seeing is the rise of identity centric attacks. Attackers aren’t breaking in—they’re logging in. Stolen credentials, MFA fatigue, and social engineering dominate modern intrusions, making identity compromise the number one attack vector globally.
Identity security is undergoing a major reinvention. Deepfakes, MFA fatigue, and AI-driven impersonation are pushing traditional authentication to its limit.
The future lies in phishing-resistant authentication, Identity Threat Detection and Response (ITDR), and AI-driven behavioral analytics that detect unusual activity instantly.
Machine identities already outnumber human ones, creating blind spots attackers can exploit. Automated discovery and governance of all identities—human and non human—will be essential. And as cyber and physical security converge, organizations will gain new ways to detect anomalies across both domains.
Agentic AI is becoming one of the most transformative forces in cybersecurity. We’re moving from reactive tools that spot known patterns to autonomous systems that learn, decide, and act in real time.
Threat actors are already using generative AI to scale their attacks—mimicking human behavior, automating reconnaissance, and bypassing traditional defenses. Defenders need the same level of automation to keep pace.
At CPX, we see agentic AI as a core pillar of cyber resilience. It allows us to embed “security by design” early in development so systems aren’t vulnerable by default. And in a region where digital sovereignty and national resilience matter more than ever, autonomous defense capabilities will be critical to protecting critical infrastructure and maintaining trust.
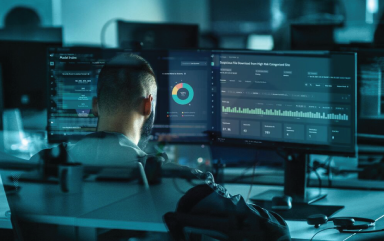
Security Operations Centers (SOCs) have never been under more pressure. Attacks unfold faster. Alerts are increasing. Environments are more complex.
Today, the AI-powered SOC is helping address these challenges. AI-enhanced detection pulls out early signals that humans would miss. It filters noise, boosts accuracy, and frees analysts to focus on higher-value activities, such as threat hunting, incident response, and strategic decision-making.
But full automation still carries risk. A false positive triggering an incorrect automated response can disrupt operations just as much as an attack. That’s why the near future lies in semi-autonomous SOCs, where AI handles repetitive tasks but humans stay in control of decisions. Strong governance and well-defined rules for AI use will be essential.
Data sovereignty laws are reshaping cloud security across the region. Organizations must now ensure their data stays under national legislative control. That means Zero Trust must be baked directly into cloud architectures, not added later.
Industrial and IIoT environments face even sharper challenges. They require security models built for industrial realities—not repurposed IT tools.
Sovereign cloud will anchor national data strategies. Legacy, perimeter-based architectures simply won’t survive in a machine speed threat landscape.
With budgets under pressure, CISOs must show that cybersecurity is not a cost but a business enabler. That means translating risk into clear business terms and focusing on measurable outcomes rather than tool accumulation.
Automation in areas like Identity and Access Management (IAM) and password self-service can reduce operational costs while improving user experience.
When security investments align with enterprise KPIs and support operational continuity, cybersecurity becomes a catalyst for innovation, not a constraint.
A future-ready security team blends technical depth with sound judgment, business acumen, and strong communication. Supported by AI automation, these teams focus on what matters most: reducing risk and keeping the organization running.
Organizations must return to the fundamentals, strengthen public–private collaboration, and build trust into every layer—across people, processes, and technology.
In 2026, cybersecurity is no longer a background function. It is a core pillar of resilience, trust, and business continuity. Organizations that recognize this—and act on it—will be the ones that remain secure, resilient, and competitive.

20 April, 2026
Identity Security Fabric: Is your IAM strategy ready for emerging...
Read now
17 April, 2026
Non-human identity governance: The silent threat in modern cloud ...
Read now

08 April, 2026
Security Performance Measurement: From compliance to confidence –...
Read now

07 April, 2026
Security Performance Measurement: From compliance to confidence –...
Read now
07 April, 2026
Bridging the gap: Integrating secure code review into the DevSecOps
Read now
02 April, 2026
Cyber in hybrid conflict: The new invisible frontline
Read now

30 March, 2026
How to write threat models that engineers actually use for strong...
Read now
27 March, 2026
Cybersecurity Documentation: Best practices for SOC, IR and secur...
Read now

26 March, 2026
The Big Shift: Making cyber agentic AI (CA2) safer – Governance, ...
Read now
10 March, 2026
vCISO vs. Advisory CISO: How to choose the right Trusted Cybersec...
Read now

06 March, 2026
The Big Shift: Demystifying Cyber Agentic AI (CA2)
Read now
25 February, 2026
Identity and Access Management in the age of AI and autonomous ag...
Read now

05 February, 2026
From Reactive to Autonomous: The rise of Agentic AI in cybersecurity
Read now

03 February, 2026
Risk prioritization in today’s evolving cyber threat landscape
Read now
21 November, 2025
Red Teaming vs. VAPT: Choosing the right test for stronger cyber ...
Read now

13 November, 2025
Compliance isn’t security: The hidden risks of a checkbox approach
Read now
29 October, 2025
GraphQL Abuse: The silent killer in API security
Read now

22 October, 2025
Securing DevOps: A GRC perspective on agility, assurance and secu...
Read now

08 October, 2025
How SOCaaS can power transformation and foster innovation in GCC
Read now

26 September, 2025
Why is red teaming a must for OT systems
Read now

19 September, 2025
UAE cybercrime statistics 2025: Key data and trends
Read now

17 September, 2025
Cyber Risk Management: Qualitative vs. Quantitative Approaches
Read now

10 September, 2025
Why AI-powered SOCs are the future of cyber defense
Read now

03 September, 2025
How AI is transforming cybersecurity and threat detection
Read now

29 August, 2025
AI vs Hackers: Who is winning the cybersecurity arms race
Read now

28 August, 2025
Why every cybersecurity team needs document version control
Read now

27 August, 2025
AI agents in cybersecurity: Your new virtual SOC team
Read now

21 August, 2025
Securing Operational Technology: Challenges and best practices
Read now
17 July, 2025
Red Teaming in cybersecurity: Why thinking like a hacker matters
Read now

21 May, 2025
What is a SCIF? Inside the CPX Secure Compartmented Information F...
Read now

21 April, 2025
Cybersecurity in the UAE: What CISOs must prioritize today
Read now

18 March, 2025
The critical role of trusted advisors in OT cybersecurity
Read now

14 February, 2025
AI Agents: The new arsenal CISOs need
Read now

27 January, 2025
Make your AI work right: A framework for secure and ethical AI
Read now

14 January, 2025
Revolutionizing SOC efficiency: The power of cyber-physical integ...
Read now

20 November, 2024
The Modern CISO Playbook: Top priorities for CISOs in 2025
Read now
30 August, 2024
Ask the Right Questions to Get Data Privacy Compliance Right
Read now

29 December, 2023
Navigating Cyberspace in 2024: A Sneak Peek into the Top Security...
Read now

14 December, 2023
Top systems integration challenges every organization must prepar...
Read now
29 August, 2023
Help ! My Facebook has been hacked
Read now

20 July, 2023
Security Product Research in the Lab: A fair chance to prove your...
Read now
20 July, 2023
The Cyber Security Conundrum: Balancing Ego and Expertise
Read now

20 July, 2023
The Internet Never Forgets
Read now

20 July, 2023
Top Cloud Security Risks and How to Address Them
Read now

20 July, 2023
Why Continuous Education, Training and Awareness are Essential fo...
Read now
02 May, 2023
A 5-Star Partner: Priming Your IT and Security Services for Success.
Read now

02 May, 2023
AI and Cybersecurity: A Tale of Innovation and Protection
Read now

02 May, 2023
How to Select a Secure Cloud Model, One Size Does Not Fit All
Read now

02 May, 2023
Making Sense of Public Ratings in Product Selection Process
Read now

02 May, 2023
Privacy Compliance: A Four-Step Approach
Read now

02 May, 2023
Securing Your Website – Gaining Online Customers’ Trust
Read now
CPX values your privacy and the security of your personal information. This Privacy Policy outlines how we use the information that we collect from you when you visit this website. Any personal information we collect from you during your use of the website will be used in accordance with this Privacy Policy.
4th floor, Z23
Mohamed Bin Zayed City
Abu Dhabi, United Arab Emirates
For immediate assistance, CALL 8002255279
©CPX 2026. All rights reserved. Privacy policy | Terms of use

Please share your details to download the report.
