02 May, 2023

From deciding how to restructure an organization to co-exist with an outsourced resource to including new projects within an existing contract, choosing a perfect technology partner might be one of the most critical decisions a CIO makes to support an organization’s growth. In this blog, Paul Lawson, Executive Director - Cyber Solutions and Delivery, CPX shares insights on common outsourcing pitfalls, barriers and new opportunities to take an IT support service from average to exceptional.
Outsourced technical support can reduce response times, offer access to sophisticated management solutions, provide multilingual support, including chatbots and AI capabilities and elevate end-user satisfaction. In other words, a wrong choice of partner can significantly impact overall business operations and success.
Here are some top insights to consider when selecting an outsourcing partner.
1. Define the Objectives: Before starting the selection process, it is essential to have a clear understanding of the outsourcing objectives, desired outcomes, commercial expectations and services to outsource from an IT service provider. CIO’s must define roles, responsibilities, mode of operations, and IT strategy, including clarity on requiring remote, hybrid or full-time end-user support. Clearly defined service level agreements (SLAs) covering response times, issue resolution and performance metrics is vital. Building them into the contract ensures the partner commits to these SLAs and associated service credits. Defining these parameters at the outset will help organizations to align with like-minded partners.
2. Evaluate Partner's Credentials: A trustworthy partner with solid track records, relevant certifications, and demonstrable experience are well-equipped to meet an organization’s requirements now and in the future. Therefore, before deciding, it is worthwhile to assess multiple outsourcing partners' technical expertise, financial stability, industry knowledge and experience in delivering similar services. This includes evaluating the outsourcing partner's security practices, certifications (for e.g. ISO 27001), and ability to comply with relevant regulations (for e.g. GDPR, HIPAA).
3. KPI is Key: When soliciting a request for proposal (RFP), generating an RFP with precise metrics such as numbers and types of servers, cloud tenants, applications and user numbers is crucial as it's generally these metrics that an outsource partner requires to generate their proposals. Effective communication is important when working with an outsourcing partner. CIOs must assess partner’s communication channels, service delivery methodology, and service credit expectations and ensure a compliance KPI matrix is included within the RFP for comparison and weightage.
4. Click Yes for Specialized Services: Outsourcing services like network management, server management, storage management and data center operations can offload the burden from internal IT teams by leveraging specialized service providers' expertise. Outsourcing cloud services, including infrastructure as a service (IaaS), platform as a service (PaaS), or software as a service (SaaS), can enable scalable and cost-effective access to advanced technologies and computing resources. As cybersecurity threats evolve, outsourcing specialized security services like threat monitoring, vulnerability assessments, security operations, and incident response can enhance an organization's security posture.
5. Scale Up or Down as Needed: CIO’s should consider scalability and flexibility when outsourcing services. Ensure the outsourcing partners can scale their services to accommodate the organization's future growth. Flexibility is a must to adapt to changing business needs and technological advancements. One essential detail to consider is to ensure that what one intends to outsource is already in "good shape. It is advisable not to outsource a problem to an outsourcing partner, as it will just be a problem that has changed hands, and the outsourcing partner will need to include additional commercials to fix them, usually within the early transition phase. Finally, ensure that an exit strategy is in place and the outsourcing partner has a detailed transition and a service improvement plan that matches the business’ IT strategy.
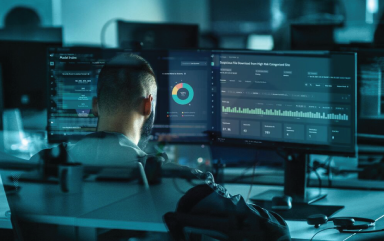
As a trusted cybersecurity solutions provider, CPX supports the region's CIOs with a range of services, including service desk and technical support, specialized security services like threat monitoring, vulnerability assessments, security operations and incident response. With the right outsourcing partner, CIOs can gain access to advanced technologies at optimum costs and, more importantly, ease the pressure off their IT and Security teams, allowing them to focus on exploring their future.

20 April, 2026
Identity Security Fabric: Is your IAM strategy ready for emerging...
Read now
17 April, 2026
Non-human identity governance: The silent threat in modern cloud ...
Read now

08 April, 2026
Security Performance Measurement: From compliance to confidence –...
Read now

07 April, 2026
Security Performance Measurement: From compliance to confidence –...
Read now
07 April, 2026
Bridging the gap: Integrating secure code review into the DevSecOps
Read now
02 April, 2026
Cyber in hybrid conflict: The new invisible frontline
Read now

30 March, 2026
How to write threat models that engineers actually use for strong...
Read now
27 March, 2026
Cybersecurity Documentation: Best practices for SOC, IR and secur...
Read now

26 March, 2026
The Big Shift: Making cyber agentic AI (CA2) safer – Governance, ...
Read now
10 March, 2026
vCISO vs. Advisory CISO: How to choose the right Trusted Cybersec...
Read now

06 March, 2026
The Big Shift: Demystifying Cyber Agentic AI (CA2)
Read now
25 February, 2026
Identity and Access Management in the age of AI and autonomous ag...
Read now

05 February, 2026
From Reactive to Autonomous: The rise of Agentic AI in cybersecurity
Read now

03 February, 2026
Risk prioritization in today’s evolving cyber threat landscape
Read now

14 January, 2026
Cybersecurity in 2026: Why identity, AI, and trust will define th...
Read now
21 November, 2025
Red Teaming vs. VAPT: Choosing the right test for stronger cyber ...
Read now

13 November, 2025
Compliance isn’t security: The hidden risks of a checkbox approach
Read now
29 October, 2025
GraphQL Abuse: The silent killer in API security
Read now

22 October, 2025
Securing DevOps: A GRC perspective on agility, assurance and secu...
Read now

08 October, 2025
How SOCaaS can power transformation and foster innovation in GCC
Read now

26 September, 2025
Why is red teaming a must for OT systems
Read now

19 September, 2025
UAE cybercrime statistics 2025: Key data and trends
Read now

17 September, 2025
Cyber Risk Management: Qualitative vs. Quantitative Approaches
Read now

10 September, 2025
Why AI-powered SOCs are the future of cyber defense
Read now

03 September, 2025
How AI is transforming cybersecurity and threat detection
Read now

29 August, 2025
AI vs Hackers: Who is winning the cybersecurity arms race
Read now

28 August, 2025
Why every cybersecurity team needs document version control
Read now

27 August, 2025
AI agents in cybersecurity: Your new virtual SOC team
Read now

21 August, 2025
Securing Operational Technology: Challenges and best practices
Read now
17 July, 2025
Red Teaming in cybersecurity: Why thinking like a hacker matters
Read now

21 May, 2025
What is a SCIF? Inside the CPX Secure Compartmented Information F...
Read now

21 April, 2025
Cybersecurity in the UAE: What CISOs must prioritize today
Read now

18 March, 2025
The critical role of trusted advisors in OT cybersecurity
Read now

14 February, 2025
AI Agents: The new arsenal CISOs need
Read now

27 January, 2025
Make your AI work right: A framework for secure and ethical AI
Read now

14 January, 2025
Revolutionizing SOC efficiency: The power of cyber-physical integ...
Read now

20 November, 2024
The Modern CISO Playbook: Top priorities for CISOs in 2025
Read now
30 August, 2024
Ask the Right Questions to Get Data Privacy Compliance Right
Read now

29 December, 2023
Navigating Cyberspace in 2024: A Sneak Peek into the Top Security...
Read now

14 December, 2023
Top systems integration challenges every organization must prepar...
Read now
29 August, 2023
Help ! My Facebook has been hacked
Read now

20 July, 2023
Security Product Research in the Lab: A fair chance to prove your...
Read now
20 July, 2023
The Cyber Security Conundrum: Balancing Ego and Expertise
Read now

20 July, 2023
The Internet Never Forgets
Read now

20 July, 2023
Top Cloud Security Risks and How to Address Them
Read now

20 July, 2023
Why Continuous Education, Training and Awareness are Essential fo...
Read now

02 May, 2023
AI and Cybersecurity: A Tale of Innovation and Protection
Read now

02 May, 2023
How to Select a Secure Cloud Model, One Size Does Not Fit All
Read now

02 May, 2023
Making Sense of Public Ratings in Product Selection Process
Read now

02 May, 2023
Privacy Compliance: A Four-Step Approach
Read now

02 May, 2023
Securing Your Website – Gaining Online Customers’ Trust
Read now
CPX values your privacy and the security of your personal information. This Privacy Policy outlines how we use the information that we collect from you when you visit this website. Any personal information we collect from you during your use of the website will be used in accordance with this Privacy Policy.
4th floor, Z23
Mohamed Bin Zayed City
Abu Dhabi, United Arab Emirates
For immediate assistance, CALL 8002255279
©CPX 2026. All rights reserved. Privacy policy | Terms of use

Please share your details to download the report.


