The role of the Chief Information Security Officer (CISO) has come a long way. What was once a position focused on managing incidents and ticking compliance checkboxes has now evolved into something much bigger. Today, CISOs have entered the boardroom, working closely with the CEO and integrating cybersecurity into strategic planning.
As we move into 2025, CISOs will face new challenges and opportunities. Here are the top priorities they must focus on to secure their organizations and drive resilience:
- Preparing for quantum computing: With the rise of quantum computing, traditional encryption methods will soon be obsolete. CISOs must start planning and implementing post-quantum cryptography solutions to protect sensitive data from quantum-enabled attacks, ensuring their encryption strategies remain future-proof.
- Using AI for better security: AI and machine learning can enhance threat detection, automate incident responses, and predict potential risks. However, CISOs must prioritize the secure development of AI models to avoid introducing vulnerabilities, ensuring robust validation and monitoring processes are in place.
- Embracing the Zero Trust architecture: With remote work and cloud services, the traditional perimeter-based security model becomes less effective. The Zero Trust model, which verifies every user and device, regardless of location, offers a modern solution.
- Staying on top of security regulations: With the global data privacy regulations landscape becoming more complex, CISOs must ensure compliance with laws such as the GDPR, CCPA, and emerging regulations. This will involve regular audits, proper data handling practices, and fostering an organizational culture of data privacy awareness.
- Securing the supply chain: Attacks targeting third-party vendors and supply chains are on the rise. CISOs need to assess the cybersecurity maturity of their partners and ensure proper risk management strategies are in place for the entire supply chain.
- Proactively hunting threats: In 2023, an estimated 25.5 percent of the world’s population was impacted by cyber-enabled fraud. Threat intelligence and threat hunting capabilities are a must have. CISOs must invest in tools to detect and mitigate threats before they cause harm.
- Enhancing patch and infrastructure management: Outdated infrastructure and neglected updates continue to be a daunting challenge for enterprises. As we move into 2025, CISOs must prioritize rigorous patch management strategies and continuous infrastructure assessments to ensure their systems remain resilient.
- Raising awareness among employees: Human error is often the weakest link in security. CISOs should advocate continuous security awareness training for all employees, ensuring they understand the latest threats, phishing tactics, and best security practices.
- Attracting and keep talent: There is a global shortage of nearly 4 million cyber professionals, according to the World Economic Forum. The focus should be on professional development programs and fostering a culture that emphasizes work-life balance and employee well-being.
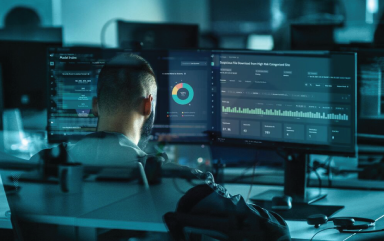
Cyber experts as you need them
With the growing complexity of cyber threats and the heightened focus on regulatory compliance, companies of all sizes are recognizing the need for a dedicated security professional to oversee their security and data protection efforts. When struggling with recruiting the expertise in house, CISO-as-a-Service can help fill the gap.
CPX’s CISO-as-a-Service offering delivers seasoned professionals who can develop and implement customized security strategies for your business. From addressing quantum risks to implementing Zero Trust, our experts collaborate with you to anticipate challenges, close security gaps, and ensure compliance with global standards.
I invite you to collaborate with CPX to build a culture of cyber transparency and resilience. Together, we can work on creating robust strategies to detect and neutralize threats before and when they arise and help your business run smoothly with minimal disruption.